Sureshot Software Vendor Incorporates Solutions to Fight .vvv File Virus
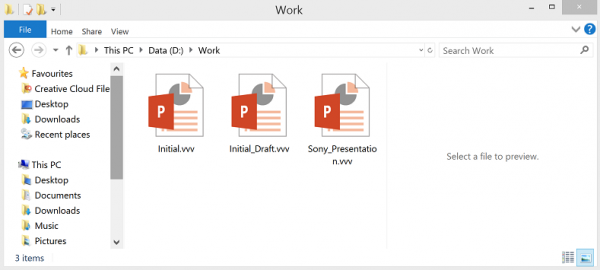
Lost Angeles, CA (PRWEB) December 10, 2015 -- The new variant of TeslaCrypt infection appends the ‘.vvv’ at the end of nearly any file at the host machine. The previous version added ‘.ccc’ at the end of infected files. There are more significant divergences as well. The newly released malware, for instance, is known to fake another ransomware called CryptoWall. The latest variant utilizes quite different encryption and propagation methods. The reason why CryptoWall virus would like to copy TeslaCrypt infection is not quite clear. Perhaps, it aims at bewildering antivirus software and experts.
The .vvv ransomware is true to basic patterns of TeslaCrypt infection. It propagates chiefly exploiting outdated software vulnerabilities. If you happen to get the parasite on your device, most likely you have not updated certain software long since.
Naturally the hackers behind the malware are not restricted whatsoever in trying alternate distribution methods. For instance, the ransomware is extremely viable in big corporate network. If stakes are high enough, that is, if hackers expect to infect thousands computers at once by hitting a large corporate network, they may try directly injecting the virus. The hackers thus will try to connect to the protected networks and install the malware into main server.
Such scenarios are possible. Again, installation through unpatched vulnerabilities prevails. However, that does not exclude other infiltration scenarios.
The malware installation is followed by complete system scan. It looks for the files of certain extension. The list of the file types the malware is to affect covers nearly all possible options. Basically, every piece of data on compromised PC is subject to the malware attack.
It is good to remove .vvv cryptic virus prior to its encoding the detected data. When it has completed its cryptic payload, private key is generated. The key is only available upon paying the ransom demanded by the hackers.
The ransom amount is to be paid in bitcoins. The sum varies within 1.5 to 2 BTC. Removal of .vvv malware does not actually decrypt the affected data. However, crooks will be crooks. There is no guarantee that by paying the ransom, which is quite high – no less than USD 300 – you will get the appropriate, if any, private key.
There is no verified way to restore the data affected by .ccc TeslaCrypt virus. It is up to user to decide whether to pay the ransom. In some cases, the amount does not matter as users are going to try everything for the sake of restoring full access to their valuable information.
On the other hand, there are plenty of high-tech options available to restore affected data. In any case, remove .vvv ransomware to prevent further damages. Reliable method for .vvv ransomware removal is available from references below. Credits: http://sureshotsoftware.com/guides/vvv/
Max Hoffman, Sureshot Software, +380 986943055, [email protected]
Share this article