451 Research: 44% of Enterprises will Increase Information Security Spending, but Staffing Obstacles Hamper SIEM Implementations
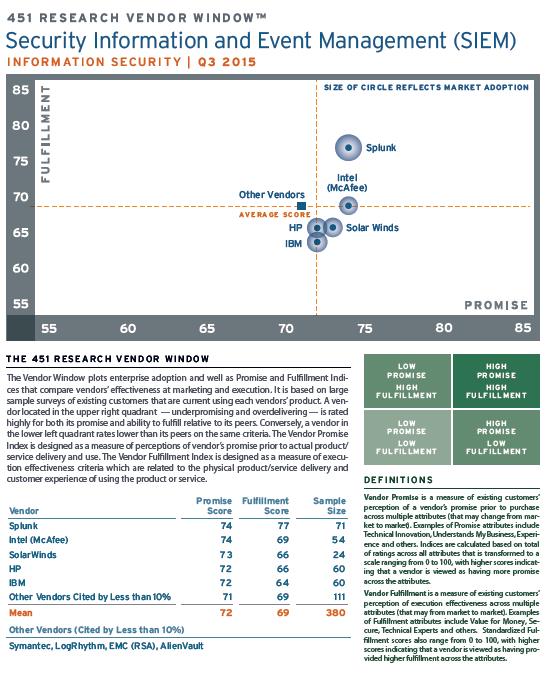
New York (PRWEB) January 07, 2016 -- According to 451 Research’s new Voice of the Enterprise: Information Security quarterly study, more than 32% of the enterprises surveyed name Splunk as their primary Security Information and Event Management (SIEM) platform provider. In the 451 Research Vendor Window™, enterprises rated Splunk highest especially for querying capability and the ease of integrating new data feeds. Intel Security is the second highest rated vendor based on evaluations from its 380 existing customers.
As expected, spending on security remains strong with 44% of enterprise security managers expecting to increase their budget in the next 90 days. Only 4% of enterprises are decreasing security spending. While security budgets are stable or increasing for almost all organizations, security managers reported significant obstacles in fully realizing the benefits of SIEM solutions because of lack of staff expertise (44.4%) and inadequate staffing (27.8%).
As one security manager in at a utilities company noted, “There is a shortage of qualified security people in the United States. I think that shortage is at very drought proportions here in [my city], and it's very difficult to find qualified people.” Given this challenge, only a little over half, 56.9%, of enterprises are able to devote more than one professional to their SIEM implementation and monitoring.
41% of respondents noted ‘hackers with malicious intent’ as their top security concern over the past 90 days, followed by navigating compliance requirements (37%). As a consequence, 23% of security managers noted that compliance requirements were a key driver in getting projects approved, second only to risk assessment cited by 25% of respondents.
"SIEM solutions hold a lot of promise as the centralized solution for unlocking all the secrets held in the logs of enterprise systems and marrying them with the use of threat intelligence”, said Daniel Kennedy, Research Director for Information Security. ”That promise comes at a cost, SIEM solutions still retain a reputation for being difficult to set up, difficult to add new feeds to, and difficult to tune. That said, their value to the enterprise security manager is increasingly understood, and while many SIEM implementations may have started out as a compliance check mark, they have transcended those roots.”
Sixteen different vendor attributes were examined in the Q4 Voice of the Enterprise: Information Security Vendor Window which plots enterprise adoption and compares and indexes vendors' promise prior to deployment as well as fulfillment after deployment. These latest findings – including a Vendor Window for Dynamic and Static Application Security Tools (DAST/SAST) – are based on responses from over 900 IT professionals, primarily in North America and EMEA, including 582 unique vendor evaluations in the third and fourth quarters of 2015.
Dynamic and Static Application Security Tools (DAST/SAST)
A second Vendor Window on both Dynamic and Static Application Security Tools (DAST/SAST) published in the study indicates open source solutions, Tenable Network Security (a vulnerability assessment tool provider that offers dynamic web application scanning), and IBM are the most widely deployed. IBM was seen as the most important vendor in the space, but it was Veracode’s and WhiteHat Security’s products that ranked highest with their customers.
Webinar
Learn more about the Voice of the Enterprise: Information Security research findings in our 'Voice of the Enterprise: Information Security Trends and Vendor Window' webinar. View the Webinar.
Voice of the Enterprise: Information Security
Published quarterly, 451 Research’s Voice of the Enterprise: Information Security provides a demand-side view of security technology adoption. These survey-driven reports are derived from 800-1,500 customer surveys and 25 in-depth interviews with senior security professionals each quarter. Learn more about Voice of the Enterprise: Information Security, as well as other Voice of the Enterprise products that cover Cloud Computing, Software-Defined Datacenters, Storage, Datacenter Facilities, and Server and Converged Infrastructure. Learn More.
About 451 Research’s Vendor Window Methodology
The Vendor Window plots enterprise adoption and Promise and Fulfillment Indices, and is typically based on 300+ unique vendor ratings per market. Only existing customers of each vendor complete the vendor evaluations. Vendors with larger circles have greater adoption in the marketplace. The Promise and Fulfillment Indices compare vendors’ effectiveness at marketing and execution. A vendor located in the upper right quadrant – under-promising and over-delivering – is rated highly for both its promise and the ability to fulfill its promise relative to its peers. Conversely, a vendor in the lower left quadrant rates lower than its peers on the same criteria.
Michael Essery, 451 Research, https://451research.com/, +1 (617) 598-7226, [email protected]
Share this article