Nabz Software Creates a Guide on How to Prevent and Remove Ransom32 – Newly Discovered JavaScript Ransomware
(PRWEB) January 11, 2016 -- Javascript enables the infection to affect virtually any operating system. Mac and Linux users are among its potential targets.
The ransomware makers rather do not deploy an attack on their victims themselves. There is a concealed webserver available in TOR network. The server offers an affiliate program. Any person that has reached the server can acquire a sample of the ransomware. The price of the transaction is 25% from each payment to be made by expected victims. The distribution system applied by the ransomware is called SaaS, that stands for software as a service. What would that mean?
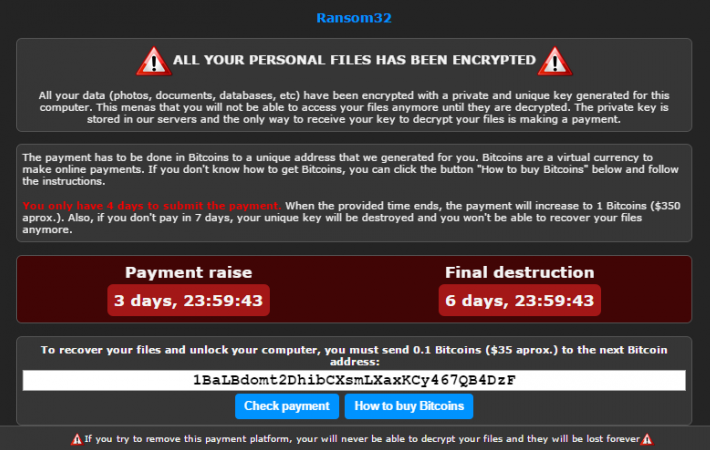
Anyone willing to affiliate with Ransom32 will be presented with a window. It is called the Affiliate Consol. The Console enables an affiliate to set parameters of the ransomware behavior. In particular, they can choose ransom amount to be paid by their victims. The selection is up to the affiliates. The developers warn the distributors: "Don't be too greedy or people will not pay."
A customized copy of the ransomware is archived and dispatched the affiliate. Even archived, it is significantly bigger than its counterparts. Extraction triples the size of malware from 22MB to 67 MB. Compare that to only 1MB average size of other ransomware.
Removal of Ransom32 is possible as it is being downloaded into your device. These are the affiliate distributors who choose the infection vector. Be that a spam email or drive-by download, it takes the time to drop the file of this significant size. In that relation, slow speed network is an advantage. Hopefully, some potential victims also have avoided the invasion as their computers do not accept files that exceed a certain size.
Another point of rescue could be the very moment of the ransomware presenting its pop-up. The affiliates may set to show it when only a small part of data on affected PC has been encrypted. Once the user is aware of the invasion, it is good to terminate all the processes at once and get rid of Ransom32 malware. Hopefully, the infection has not blocked any crucial data yet.
Removal tips include:
1) Get auto cleaning and recovery software.
2) Use Previous Versions feature of Windows.
3) Utilize Backups.
The removal process is described in more detail here: http://nabzsoftware.com/types-of-threats/ransom32
Max Hoffman, Nabz Software, +380 986943055, [email protected]
Share this article