Innovation Update: Fortscale 2.7 Reveals New Ways to Detect Insider Threats
San Mateo, California (PRWEB) August 15, 2016 -- Fortscale Security Ltd., the innovative pioneer in machine-learning-based user behavior analytics for security (UEBA) and named to the list of “Cool Vendors” in the “Cool Vendors in UEBA, Fraud Detection and User Authentication, 2016” report by Gartner, Inc., today introduced the newest version of its flagship product. Fortscale 2.7 features new use cases, supported data sources, and new user experience that makes it easier for security professionals to find and stop insider threats automatically.
Organizations are having difficulty protecting themselves from growing and evolving security threats, but there is hope. In “The Fast-Evolving State of Security Analytics, 2016” report, Gartner stated: “Rapid advances in analytics and machine learning are quickly changing the security landscape. Security managers having problems detecting malicious events should invest in security analytics to enable better threat detection and higher security staff productivity.”
“Securing your organization from insider threats cannot be done with first generation UEBA, rules-based security solutions or SIEMs, as they only address known threats,” explained Idan Tendler, Co-founder and CEO, Fortscale. “Whereas Fortscale’s innovative, second generation technologies and analytics help security analysts catch the unknown behavior of users and entities in the enterprise that pose a security threat.”
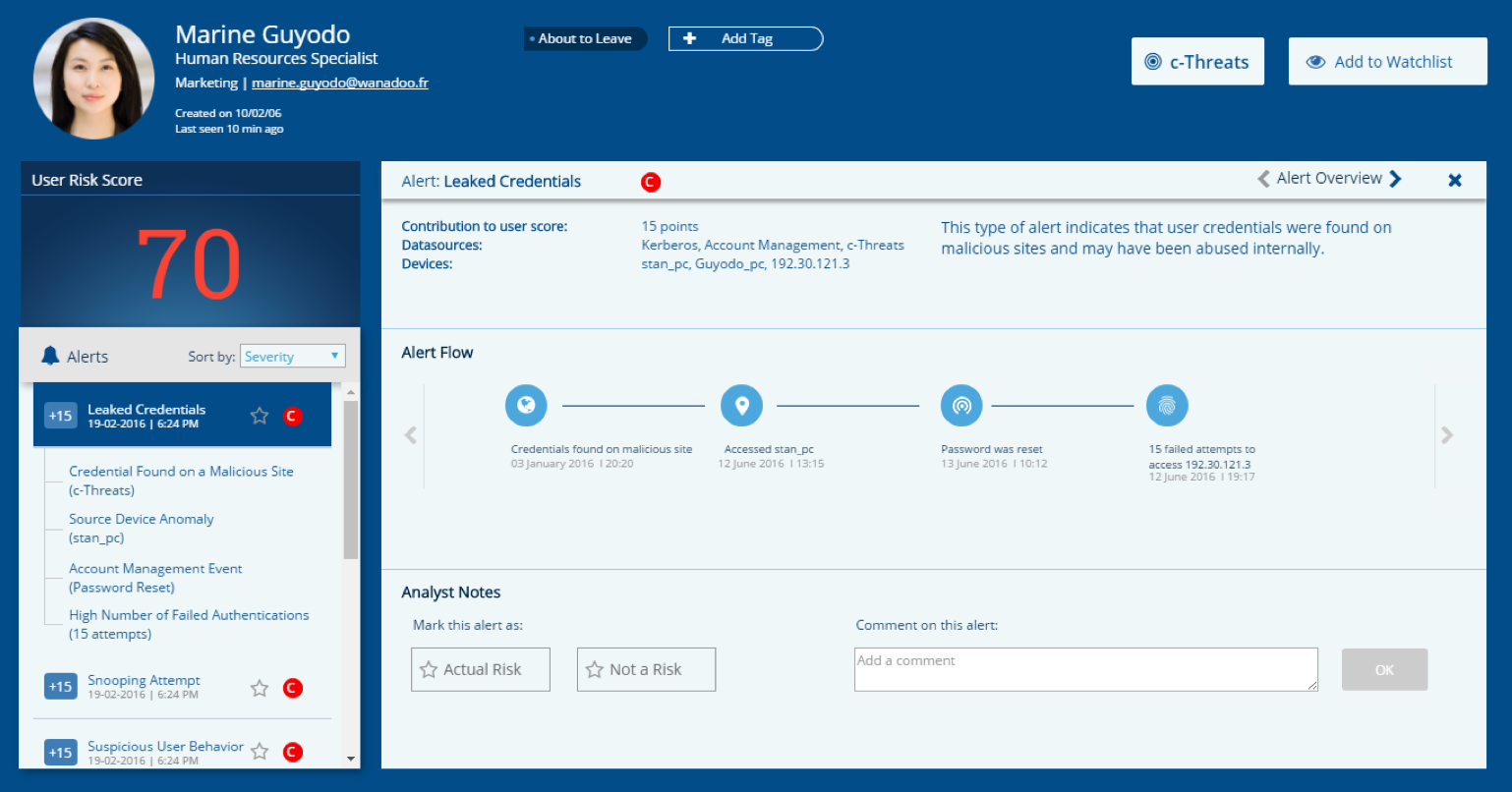
New: Detecting Insider Credentials Compromised on the Dark Web
It has never been easier for disgruntled employees to harm their employers. The Dark Web has become a place for disgruntled employees to sell information for profit or revenge. The buyers of the credentials then have the ability to get into the company’s network with little chance of detection – until now.
Fortscale has built a solution to detect when insider credentials have been compromised on the Dark Web. Fortscale 2.7 consumes external threat feeds that roam the Dark Web in search for compromised enterprise usernames and passwords. When a monitored enterprise credential is identified on the Dark Web, it is instantly streamed into Fortscale and is correlated with risky behavior found within the corporate environment. Fortscale alerts SOC analysts that a trusted user's credential was found and was possibly abused by a malicious actor, so that counter measures can be taken.
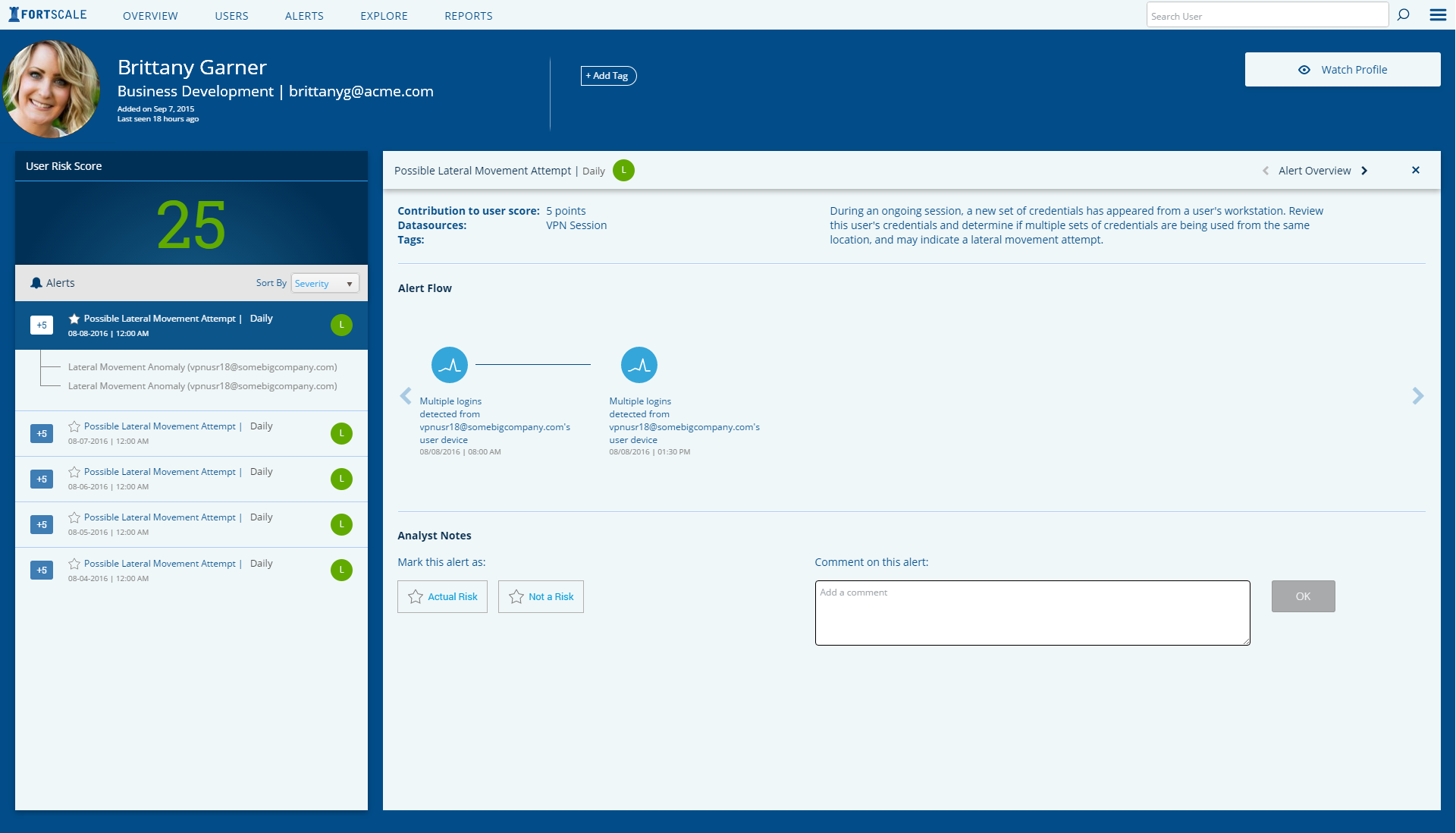
New: Detecting Remote Lateral Movement
Stealing or hijacking legitimate employees’ credentials is known to be one of the main tools used by attackers who would like to infiltrate into the enterprise. Once attackers are inside the network, they are usually leveraging their credentials in their lateral movement or even exfiltration. Fortscale has a unique ability to identify when abnormal access from a remote location occurs. Incoming remote connections are inspected by Fortscale to detect when a username and password are used from the same hostname to access other network assets and may indicate a possible lateral movement attempt. This new ability has already helped Fortscale’s customers detect these malicious actions in time and remediate them.
New: Data Sources and User Experience and Interface
In addition to processing access and SIEM logs to find anomalies, Fortscale 2.7 leverages its new Generic Data Source framework (GDS) to provide out-of-the-box support for several new data source types, including Network DLP, Secure Web Gateway, and Cisco ACS.
Fortscale 2.7 also has a completely redesigned user experience and interface that introduces an entirely new method of investigation, incorporating the existing machine-learning based user data with new workflows, upgraded visualizations and widgets. This makes it easier for security professionals to identify, investigate and stop insider threats.
For more information about Fortscale 2.7, you can download the data sheet here.
Fortscale’s research and development efforts continue to garner recognition for fundamental advancements in UEBA technology. Fortscale was named the “2016 Leader in Threat Detection” by Cyber Defense Magazine and a “Cool Vendor” in the “Cool Vendors in UEBA, Fraud Detection and User Authentication, 2016” report by Gartner, Inc.
About Fortscale
Fortscale ends insider threats with a totally new generation of rule-free, autonomous behavior analytics based on machine learning. With no rules to set up, Fortscale’s user behavior analytics engine starts getting smarter the second you turn it on. Fortscale models your users and systems autonomously, on-the-fly. Fortscale spots anomalous behavior quickly, accurately and doesn’t need constant “babysitting.” It might sound like magic, but it’s mostly just really good math – and only Fortscale has it. Backed by Intel Capital and Blumberg Capital, Fortscale ends insider threats, lowers analyst stress-levels and makes your whole security operation work a whole lot better. For more information, visit fortscale.com.
Disclaimer
Gartner does not endorse any vendor, product or service depicted in our research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Gartner “Cool Vendors in UEBA, Fraud Detection and User Authentication, 2016” report by Andrew Walls, Brian Reed, Avivah Litan, Sandy Shen, and Craig Lawson, 02 May 2016
“The Fast-Evolving State of Security Analytics, 2016” report by Avivah Litan, Toby Bussa, Eric Ahlm, 04 April 2016
Both reports are available to subscribers at Gartner.com.
Lynn Strand, Fortscale Security, Ltd., http://fortscale.com, +1 (415) 689-6127, [email protected]
Share this article