KnowBe4 Issues Actions to Protect Against the Global Outbreak of WannaCry Ransomware Ransomware Rampage
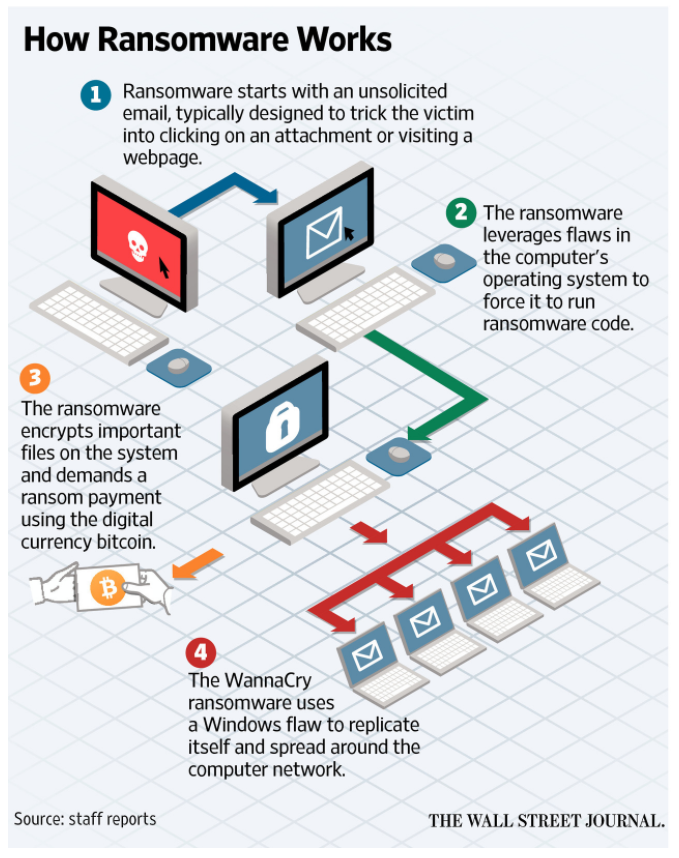
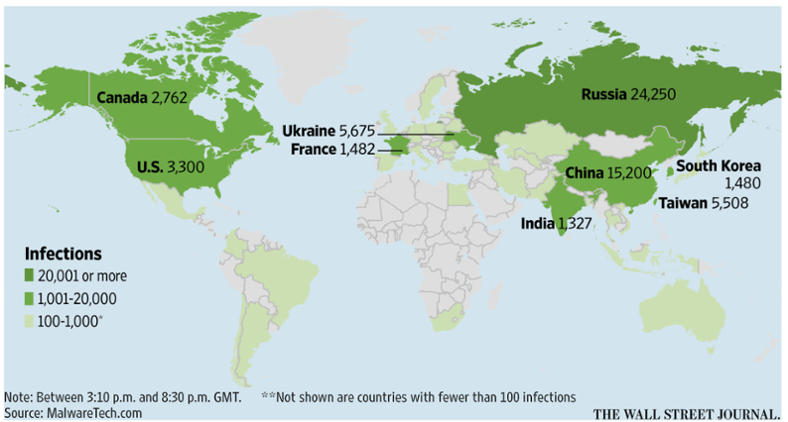
Tampa Bay, FL (PRWEB) May 15, 2017 -- From healthcare groups like the NHS in the UK to Spanish telecom company Telefonica, hundreds of organizations have been ravaged by an unprecedented ransomware attack from a strain called “Wana Decrypter” or “WannaCry.” This worm, using leaked NSA cyberattack code, has infected hundreds of thousands of computers in more than 150 countries since Friday, suspending all kinds of critical systems.
Stu Sjouwerman, CEO of KnowBe4 the provider of the world’s most popular security awareness training and simulated phishing platform, issued an alert stating, “Over the weekend, new samples of WannaCry emerged without the initial kill switch. This means the attackers resumed their campaign even though the MalwareTech security researcher accidentally cut off the original wave. WannaCry’s persistence is only the beginning. It is indicative of the sophistication of ransomware and its ability to severly impact critical infrastructures.”
Sjouwerman laid out all the updated information about WannaCry, how to detect it, a central base of links to patches required, workarounds if IT cannot patch along with other pertinent information so IT can keep its users educated.
Sjouwerman advised:
Eight Ways to Protect Against WannaCry, (apart from having weapons-grade backups):
1. Check your firewall configuration and make sure no criminal network traffic is allowed out, and disable SMB1 on all machines
2. Wipe the machine and re-image from bare metal, for WannaCry and any ransomware infection.
3. Install Secure Email Gateway (SEG), that does URL filtering and make sure it's tuned correctly.
4. Patch endpoints, OS and 3rd-party applications very regularly.
5. Ensure endpoints and web-gateway have next-gen, frequently updated (a few hours or shorter) security layers.
6. Identify users that handle sensitive information and enforce some form of higher-trust authentication like two-factor authentication.
7. Review internal security policies and procedures, specifically related to financial transactions to prevent CEO fraud.
8. Deploy new-school security awareness training, which includes simulated social engineering tests via multiple channels, not just email.
“This nasty crypto-pandemic appears to have started with phishing, and could have been avoided if users would have been well-trained on spotting the red-flags. Employees are your last line of defense and need to be trained to avoid being victims of social engineering through phishing attacks,” added Sjouwerman.
KnowBe4 further recommends checking the network to get a quick look at the effectiveness of existing protections using its no-cost Ransomware Simulator tool which simulates ten scenarios to show whether a workstation is vulnerable to infection.
For more information on how to spot social engineering red flags, visit: https://www.knowbe4.com/what-is-social-engineering/ and visit http://www.knowbe4.com to find out more about how you can strengthen your last line of defense and create a human firewall.
About KnowBe4
KnowBe4, the provider of the world’s most popular integrated new school security awareness training and simulated phishing platform, is used by more than 9,500 organizations worldwide. Founded by data and IT security expert Stu Sjouwerman, KnowBe4 helps organizations address the human element of security by raising awareness of ransomware, CEO Fraud and other social engineering tactics through a new school approach to security awareness training. Kevin Mitnick, internationally recognized computer security expert and KnowBe4’s Chief Hacking Officer, helped design KnowBe4’s trainings based on his well-documented social engineering tactics. Thousands of organizations trust KnowBe4 to mobilize their end-users as the last line of corporate IT defense.
Number 139 on the 2016 Inc 500 list, #50 on 2016 Deloitte’s Technology Fast 500 and #38 in Cybersecurity Ventures Cybersecurity 500. KnowBe4 is based in Tampa Bay, Florida. For more information, visit http://www.knowbe4.com and follow Stu on Twitter at @StuAllard.
Kathy Wattman, KnowBe4, http://www.knowbe4.com, +1 (727) 474-9950, [email protected]
Share this article