ID Integration Announces New Solutions to Combat Barcode Security Threat Takedowns
MUKILTEO, Wash. (PRWEB) March 13, 2018 -- What is the possibility of a cyber attack on your operating system? Consider the fact that barcode scanners act as a secondary keyboard to your computer. Any astute hacker can infiltrate your system with an errant Open Windows Run Command—With just some 50 keystrokes, the hacker swings open the door to your computer and network.
Once the cyber thief unlocks your system, your sensitive data floods the Deep Web marketplaces. Imagine the harm done to the release of personal information, trade secrets, and classified documents. Imagine the harm done to the leakage of info about products and parts in development. Imagine the loss of your company’s reputation. And imagine the lost revenue due to extended downtime, OS system restoration, and time and energy needed to rebuild your website, databases, and networks. The very real result is a huge financial impact from the direct loss of government contracts.
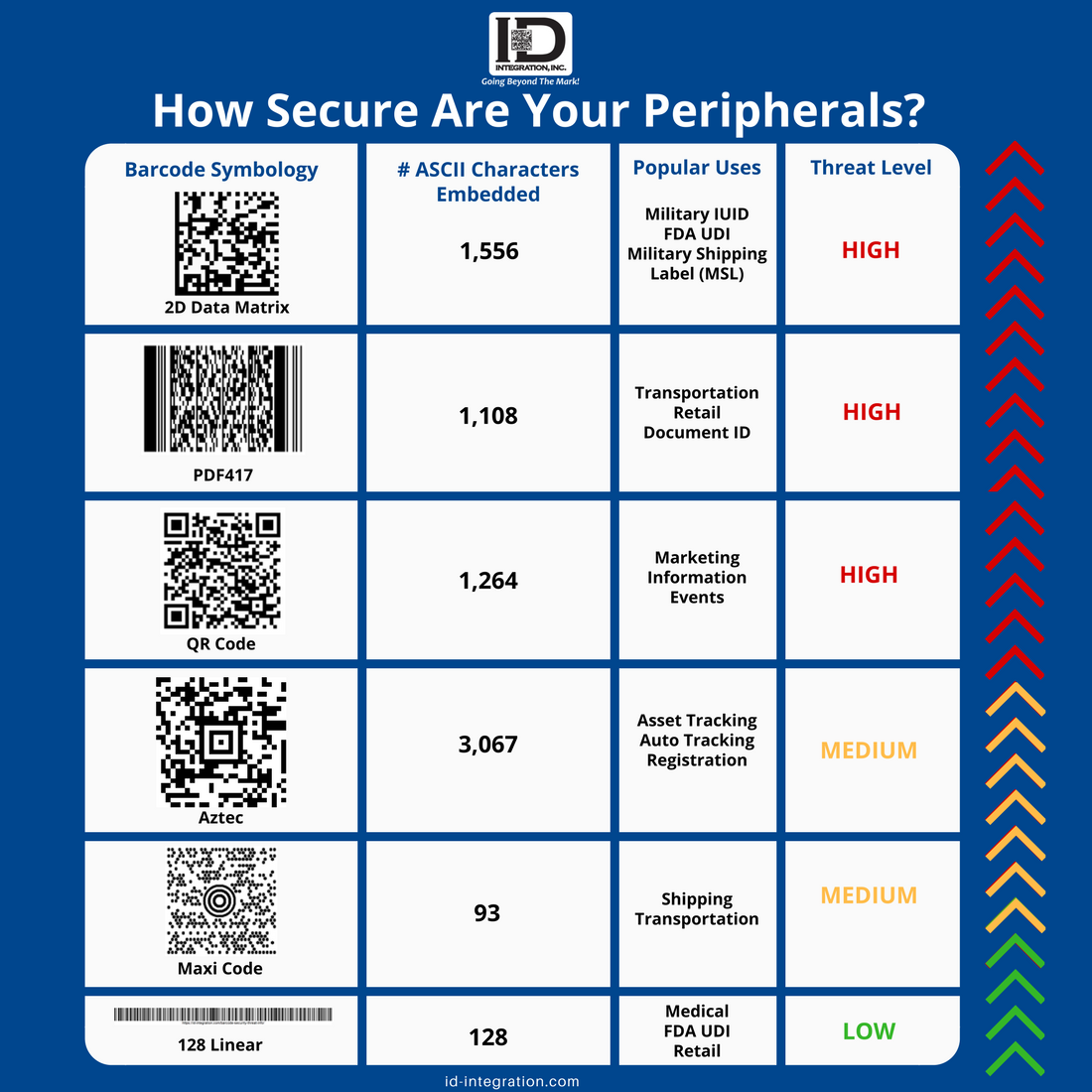
These threats are very real, whether the malicious system commands are hiding within FDA UDI labels, DoD IUID marks, free form QR codes, PDF417 barcodes, or other forms of 2D Data Matrix symbologies. No barcode is exempt from a cybersecurity TKO.
The barcode experts at ID Integration imagined just these scenarios. Our BarCode OS ® enabled scanners continue to offer the World’s only firewall protection to halt malicious barcode commands. Additionally, our technology reads any supported barcode, even malicious codes, without the risk of infecting your computer and network. Plus, this exclusive BarCode OS ® hardware is impervious to tampering—The patent-pending security filter cannot be disabled.
Awareness is the first step to blocking a potential security threat. To this end, the ID Integration cybersecurity team is offering two new solutions: Education and Consultation.
Cybersecurity Education
Knowledge is power: When you know what you’re up against, you can create an action plan to avoid a data breach. Our free white paper, “Is a Barcode Security Threat Looming in Your Company’s Future?” introduces you to the latest news and preventative measures in barcode cybersecurity. You’ll discover answers to:
• How do hackers break into operating systems so easily?
• How safe are your barcode readers?
• What are the consequences of a barcode security breach?
• What happens to your data during a security breach?
• Which industries are impacted by barcode security breaches?
• What is your legal responsibility in the event of a data breach?
Prevent a barcode cyber attack from happening in the first place—Download this white paper at our new web page dedicated to avoiding the repercussions of data breach fallout.
Cybersecurity Consulting
Here at ID Integration, our new premium cybersecurity consulting service is modeled after our renowned consulting services for system integration of barcode marking and labeling, verification, and registration processes.
We pride ourselves on our wide expertise across the many industries that depend upon safe data collection using barcode readers—the manufacturing sector, aerospace contractors, suppliers of medical devices bearing FDA UDI labels, and contractors that manufacture DOD IUID compliant parts.
ID Integration makes it our #1 job to create and promote a secure environment for collecting and storing sensitive data. To this end, our new professional cybersecurity consulting services include:
• Detailed Needs Analysis—We measure your vulnerability and risks. We take the time to review and understand your company’s security posture without impeding your daily operations. Our comprehensive cyber evaluation includes penetration tests for internal and external security weaknesses.
• Risk Profile Creation—After we assess your security capabilities, we’ll recommend actions to seal up vulnerabilities. Expect guidance that incorporates BarCode OS ® technology and artificial intelligence (AI) tools and processes to secure your workplace.
• Ongoing IT Risk Management Strategy—Cybersecurity evaluation is not a static problem-solver. Hackers continually invent new ways to thwart system security measures. As your independent IT security consultants, ID Integration builds a custom strategy to stay one step ahead of hackers. Receive a cyber policy and plan containing your three-fold master plan: configuration, design, and remediation for your operating systems. We develop an IT risk management and compliance roadmap from the office to the shop floor.
• On-Site Cyber Consulting —ID Integration goes beyond providing a report filled with recommendations. We’ll help you execute your operational procedures, IT engineering, and security policy for incident response and security deployment. We offer hands-on instruction for threat identification, management of security processes, and security authorization fundamentals.
Our goal is to address security vulnerabilities BEFORE the cyber criminals find them. We’ll partner with your IT team to search for application design flaws, errors in configuration, and software bugs. Then, we’ll apply cybersecurity solutions to ensure the integrity, availability, authorization, and confidentiality of your data and information.
ID Integration’s new barcode security consultation services are now live! Contact us at 425-438-2533 to get started with a customized needs analysis and recommendations to implement solutions to prevent security breaches.
Gary Moe, ID Integration, Inc., https://id-integration.com/, +1 (425) 438-2533, [email protected]
Share this article