Flashpoint's new 2026 capabilities empower teams to move beyond visibility to defensible action by connecting adversary activity to business priorities, assets, and investigations.
SAN FRANCISCO, March 23, 2026 /PRNewswire-PRWeb/ -- RSA Conference 2026 -- Flashpoint, the global leader in threat intelligence, today announced a suite of capabilities designed to bridge the gap between threat data and organizational impact — including threat-informed External Attack Surface Management (EASM), Business-Aligned Priority Intelligence Requirements (PIRs), and a Managed Attribution browser. Revealed during the RSA Conference 2026, these innovations shift the focus from simply seeing threats to operationalizing intelligence by connecting adversary activity directly to the people and assets organizations must protect.
"The industry has reached a tipping point where security teams are drowning in data that fails to align with their most important business requirements and decisions," said Josh Lefkowitz, Co-Founder and CEO of Flashpoint. "Visibility alone is no longer a victory; it's a baseline. By connecting underground adversary activity to an organization's specific attack surface and strategic requirements, Flashpoint is raising the bar beyond passive observation. We are enabling defenders to stop asking 'what do we own' and start answering 'what do we fix first, and why,' turning raw data into an engine for risk reduction at speed."
Threat-Informed External Attack Surface Management (EASM)
Traditional attack surface tools identify what an organization owns, but they often leave security teams buried under long lists of exposed services and CVEs without the necessary context to prioritize them.
To address this, Flashpoint is launching threat-informed External Attack Surface Management (EASM)evolving EASM from simple asset discovery to threat-informed prioritization. Flashpoint EASM will continuously discover internet-facing assets such as domains, subdomains, and IPs then automatically map them to Flashpoint's proprietary vulnerability intelligence. This enables teams to stop guessing and start focusing on the specific vulnerable software and high-risk exposures that threat actors are actively targeting.
Business-Aligned Priority Intelligence Requirements (PIRs)
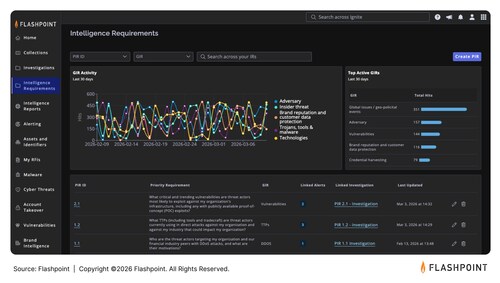
Many teams are held back by a lack of structural clarity. Without defined priority intelligence requirements, it is difficult to determine what the business actually needs or how to support it consistently. As threat intelligence becomes increasingly critical to the modern enterprise, organizations must ensure a clear connection between technical activity and Board-level imperatives. This shift necessitates the use of Priority Intelligence Requirements (PIRs), which provide an objective framework for organizing intelligence and measuring its impact. By moving from "intelligence when needed" to "intelligence with purpose," teams can transform scattered activity into a structured, defensible program that aligns with executive expectations.
To resolve these structural disconnects, Flashpoint is introducing in-platform Intelligence Requirements in May to define, formalize, and operationalize Priority Intelligence Requirements (PIRs). By tying every alert, investigation, and output back to a defined risk priority, organizations can ensure their intelligence programs are measurable, defensible, and strategically aligned with business decisions.
Managed Attribution Browser
Investigating criminal communities and malicious infrastructure carries significant operational risk, often requiring analysts to manage heavy technical overhead to set up secure, isolated environments. To accelerate research and reconnaissance, Flashpoint is expanding its Managed Attribution capabilities with a new, non-persistent investigation environment. This solution allows analysts to instantly spin up an anonymous, disposable browser to engage in underground communities and open suspicious links without risk of compromising their identity or infrastructure.
For example, a security analyst can use this secure, isolated environment to safely interact with a threat actor on an encrypted messaging platform or open a suspicious file found on a ransomware leak site, all without exposing their organization's network or their own digital identity to the adversary.
By eliminating configuration friction, analysts can move from setup to active investigation in seconds.
Meet Flashpoint at RSA 2026
Flashpoint invites attendees to visit Booth S-3341 for a sneak peek of these upcoming features and to learn how primary-source intelligence can strengthen their security posture. For more information or to schedule a meeting, please visit https://flashpoint.io/events/rsac-conference/.
Frequently Asked Questions
What is Flashpoint showcasing at RSA 2026?
Flashpoint is showcasing how its primary-source threat data connects directly to business assets and priorities. At the booth, attendees can get a sneak peek of the upcoming in-platform Priority Intelligence Requirements (PIRs), which formalize how security teams tie investigations to business risk. Flashpoint will also be discussing the upcoming general availability of threat-informed EASM for asset discovery and risk prioritization, alongside the Flashpoint Managed Attribution Browser, designed for secure underground research.
What is Flashpoint Threat-Informed EASM?
Flashpoint threat-informed External Attack Surface Management (EASM) goes beyond listing owned assets to identify which vulnerabilities on those assets are high-risk based on Flashpoint's real-world adversary activity data and underground discussions.
How do Flashpoint Priority Intelligence Requirements (PIRs) help security teams?
Flashpoint PIRs provide a formal in-platform structure that ties security alerts and investigations to specific business risks. This helps teams move away from reactive "activity-based" work and toward "decision-based" intelligence that is defensible to executive stakeholders.
What are the benefits of the Flashpoint Managed Attribution browser?
The Flashpoint Managed Attribution browser allows threat analysts to research the Deep and Dark Web safely using a disposable, anonymous environment. This prevents the analyst's identity from being exposed and protects the corporate network from malware while conducting underground research.
How does Flashpoint's new offering support a Continuous Threat Exposure Management (CTEM) framework?
Flashpoint facilitates the CTEM lifecycle by providing the primary source data necessary to move beyond traditional point-in-time scanning. EASM enables organizations to start focusing on the specific vulnerable software and high-risk exposures that threat actors are actively targeting.
About Flashpoint
Flashpoint is the leader and largest private provider of threat data and intelligence. We empower mission-critical businesses and governments worldwide to decisively confront complex security challenges, reduce risk, and improve operational resilience amid fast-evolving threats. Powered by Flashpoint Primary Source Collection, our proprietary approach to collecting intelligence directly from the digital spaces where threats originate, the Flashpoint Ignite platform delivers unmatched depth, speed, and relevance from open and hard-to-reach sources, enriched by human expertise and scaled by AI. Our solutions span cyber threat intelligence, vulnerability intelligence, geopolitical risk, physical security, fraud, and brand protection. The result: our customers safeguard critical assets, avoid financial loss, and protect lives. Discover more at flashpoint.io.
Join the conversation. Follow us on LinkedIn and X.
Media Contact
Kari Walker, RedIron PR for Flashpoint, 1 7039288886, [email protected]
SOURCE RedIron PR for Flashpoint


Share this article