NEW YORK, Feb. 28, 2019 /PRNewswire-PRWeb/ -- Hysolate, pioneer of secure software-defined endpoints, today revealed results of its 2019 Privileged Access Workstations (PAW) survey. Key findings include that 87 percent of cybersecurity professionals believe separating privileged environments from corporate, internet-exposed environments is highly critical for protecting sensitive information. It also found that time-consuming access processes and the inability to install apps, browse the web or plug in external devices, are key implementation roadblocks. The survey was conducted by Cybersecurity Insiders and queried approximately 200 security professionals.
"Privileged users are targeted by cyberattackers because they have direct access to an enterprise's crown jewels. The good news, according to the PAW survey, is that the overwhelming majority of enterprises believe protecting these users and data resources is a priority," said Tal Zamir, CEO and co-founder of Hysolate. "However, common methods to secure privileged access, such as using separate workstations or jump hosts, often have an adverse effect on user productivity or still allow attackers to gain privileged access. Enterprises clearly need a way to have trusted privileged access without compromising user performance."
According to Neil Macdonald, VP and Distinguished Analyst at Gartner, CISOs should "focus on projects that reduce the most amount of risk and have the largest business impact." He said a number 1 priority is to make it harder for attackers to access privileged accounts.
Highlights of Hysolate's 2019 Privileged Access Workstations Survey
- Protecting Privileged Environments is Highly Critical
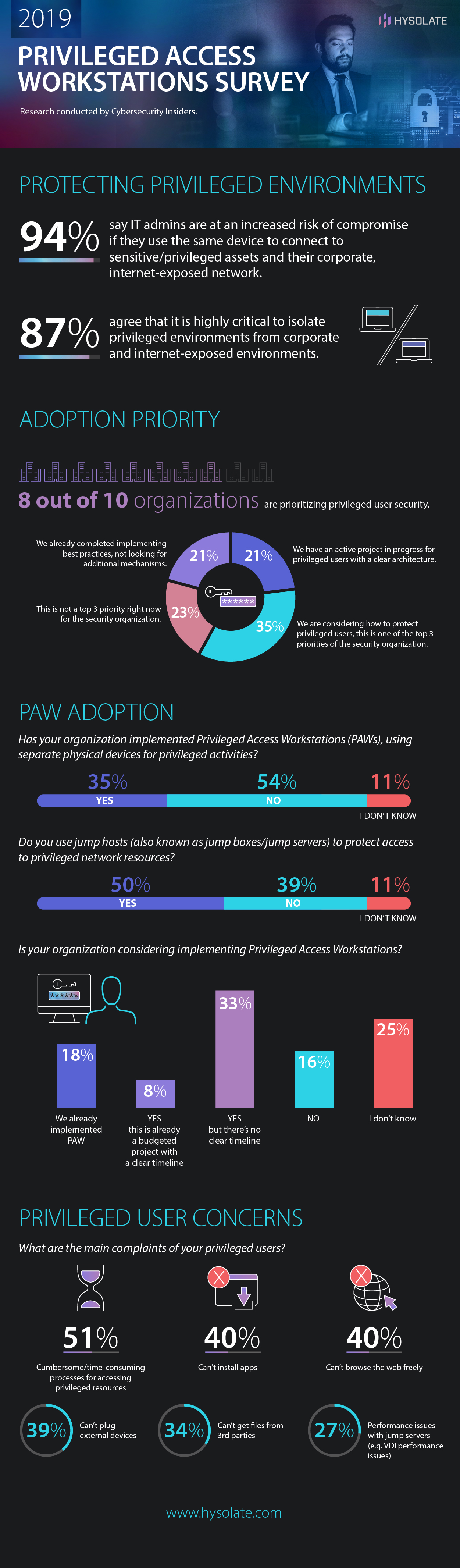
87 percent of cybersecurity professionals agree that isolating privileged environments from general corporate and internet-exposed environments is highly critical.
- Nearly 80 Percent of Respondents Have Already or Are Planning to Implement PAW
42 percent of organizations have completed or are actively implementing additional security measures for privileged users. In addition, 35 percent say doing so is a top 3 priority and are evaluating how to accomplish this.
- Separate Workstations and Jump Hosts Have Some Adoption
94 percent of respondents say IT admins are at increased risk of compromise if they use the same device to connect to sensitive/privileged assets and their corporate, internet-exposed network. This may explain why, according to the survey, 35 percent have implemented PAW using separate physical devices, and 50 percent use jump hosts/jump servers to protect access to privileged network resources.
- Privileged Users Are Concerned about Complexities and Productivity Loss
Many privileged users are frustrated by the limitations imposed by existing security measures. 51 percent cite cumbersome, time-consuming processes for accessing privileged resources, while 40 percent complain that they can't install apps or browse the web freely. More than a third take issue with not being able to plug in external devices (39 percent) or get files from third parties (34 percent).
- PAW Challenges Impede Adoption
33 percent of organizations are considering implementing some form of PAW but have no clear timeline, while 16 percent currently have no plans in place.
There are multiple ways to secure access to privileged accounts, including Hysolate's virtual air gap approach that enables multiple segregated environments on the same end-user device. For more information on how cybersecurity professionals view PAW challenges and opportunities, click here to download a free copy of the Hysolate 2019 Privileged Access Workstation Survey.
About Hysolate
Hysolate pioneered software-defined endpoints, the most innovative way to secure end-user devices and boost user productivity. The solution seamlessly splits devices into fully isolated, segregated environments by leveraging virtualization and provides protection below the operating system. Customers include leading financial, technology and services enterprises worldwide. Hysolate's team includes IT and cybersecurity experts who are veterans of VMware, Microsoft, CyberArk and Unit 8200 (Israel's NSA). The company was launched by Team8, a cybersecurity think tank, is privately held, and has headquarters in Tel Aviv and New York. Visit us at http://www.hysolate.com and follow us on LinkedIn and Twitter @HysolateNow.
SOURCE Hysolate
Share this article